As the technological capabilities of ADAS and AI-driven systems continue to mature, the barriers to mass adoption of autonomous vehicles are no longer primarily technical. Real–world applications, ranging from robotaxis and logistics delivery robots to autonomous truck fleet operations are already emerging through industry partnerships and evolving regulatory frameworks.
Increasingly, the primary barrier to autonomous vehicle adoption is shaped by user perception rather than technological readiness. Psychological and behavioral factors are beginning to influence demand, with public sentiment playing a critical role in determining adoption trajectories.
Even a single incident or news of investigations by regulatory bodies can trigger widespread concern, resistance, and skepticism. These reactions reinforce the perception that autonomous systems should not operate on public roads, creating a mental barrier to full autonomy, and in turn, slowing investment and business development initiatives.
Understanding this behavioral dimension is critical. The key question for mobility innovators now extends to whether users will continue to trust the system when something goes wrong. This shift calls for cyber resilience — the ability to maintain secure and reliable operations even under disruption — to serve as a foundation for sustaining user trust and enabling scalable adoption in a smart mobility ecosystem.
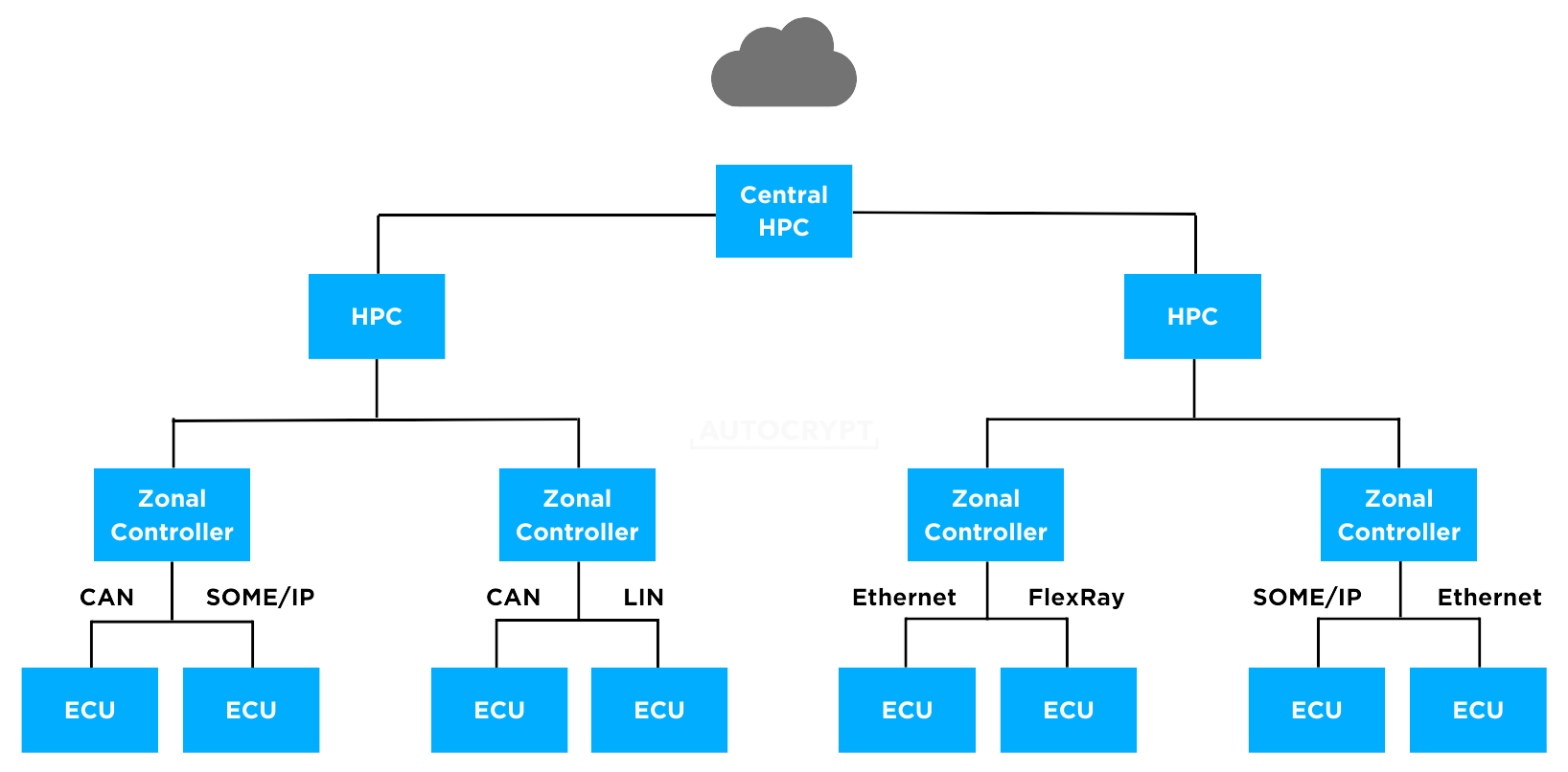
Complexity of Modern Vehicle Systems
Mobility is no longer a standalone product; it is evolving into an interconnected system of systems. The boundaries between mobility domains are increasingly blurred, with vehicles exhibiting robotic characteristics and distinctions between various modes of transportation gradually converging.
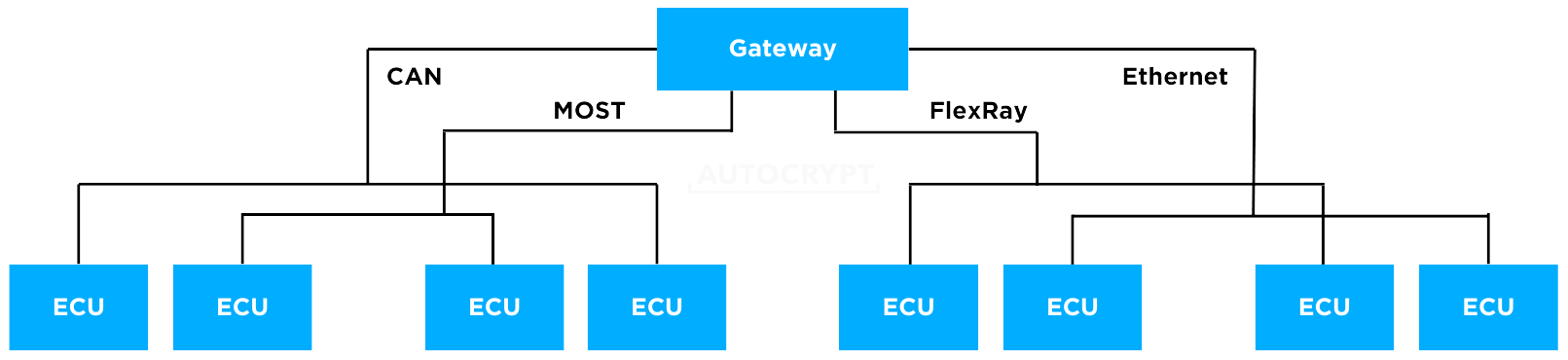
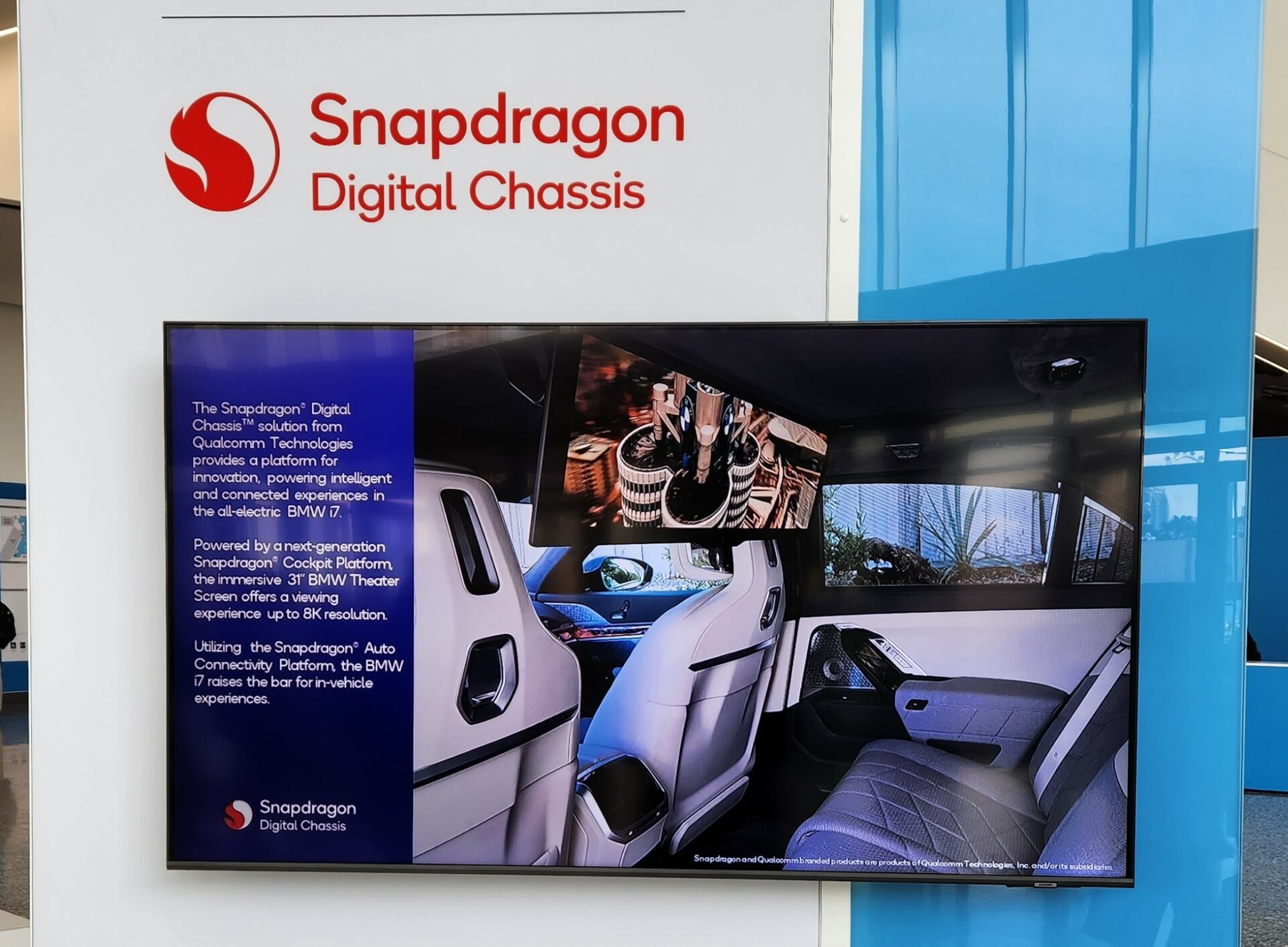
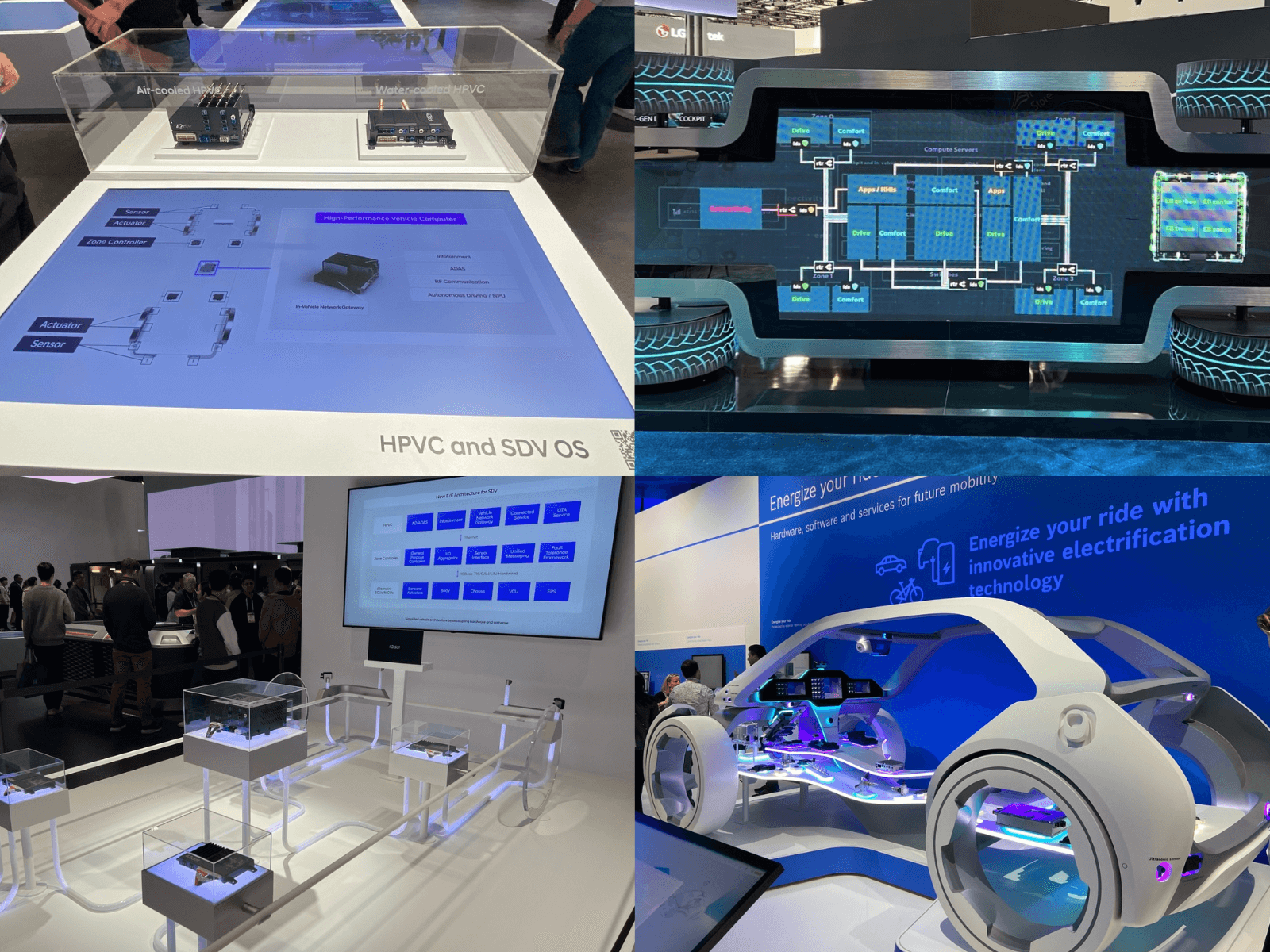
As vehicle platforms evolve — from connected cars to software-defined vehicles, and ultimately AI-driven systems — their internal architecture has expanded significantly. What was once centered on hardware, electrical, electronic, and software components now extends to include on-demand applications, service-based functionalities, and AI-powered capabilities.
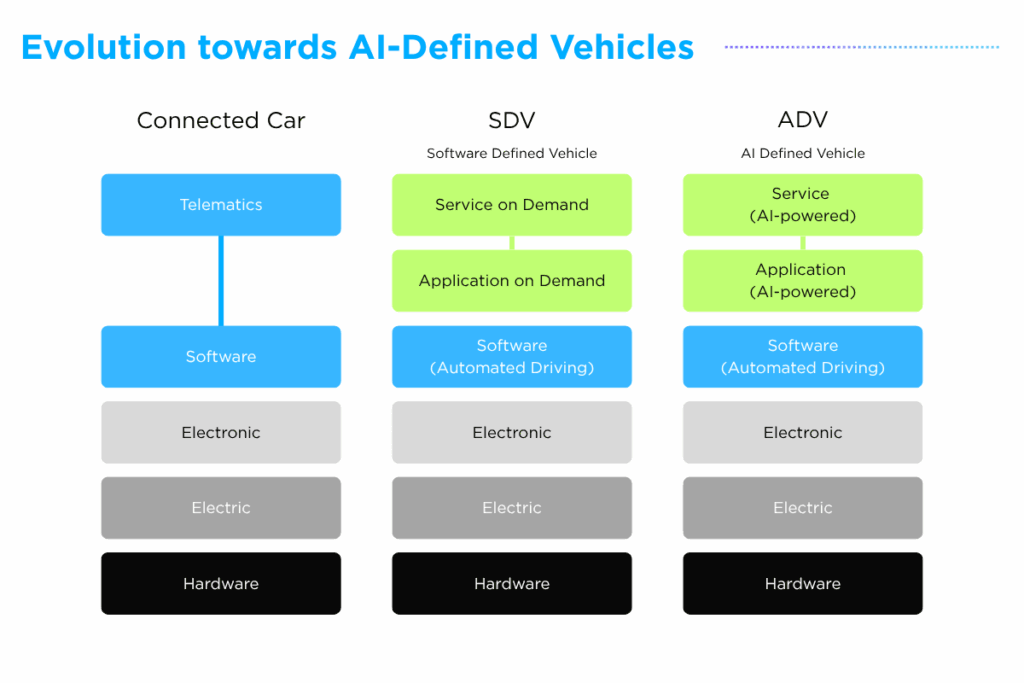
While this evolution enables greater functionality, it also introduces increased system interdependencies and, consequently, higher levels of unpredictability. This transformation is not occurring in isolation, but driven by a self-reinforcing cycle.
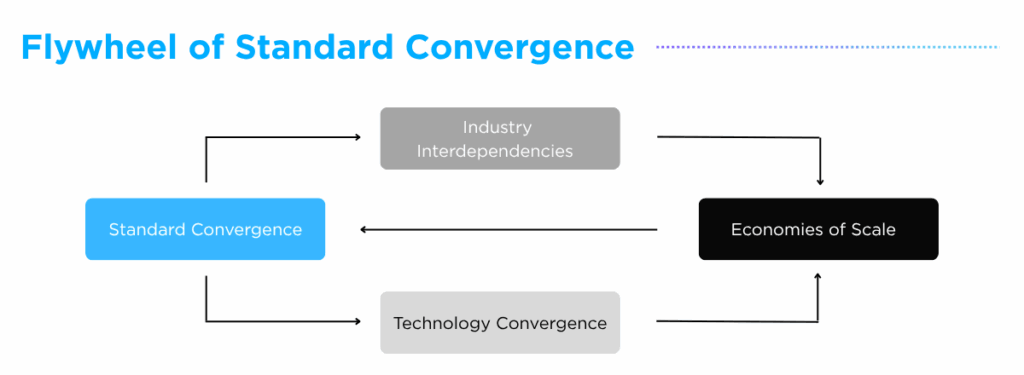
- Standard Convergence: Common frameworks and regulations align across industries, enabling interoperability and shared development baselines.
- Technology Convergence: Shared architectures, platforms, software stacks are adopted across domains, accelerating cross-industry innovation.
- Industry Interdependencies: Automotive, robotics, infrastructure and adjacent sectors become tightly interconnected, increasing system-level reliance.
- Economies of Scale: Wider adoption reduces costs and barriers, enabling faster deployment and reinforcing shared ecosystems.
This cycle continuously amplifies system connectivity and complexity, ultimately resulting in tightly coupled environments where disruptions are difficult to isolate and contain. They must be designed to function reliably within uncertain and dynamic environments. This requires not only protection against threats, but also the ability to maintain predictable behavior, ensure operational continuity under disruption, and support consistent system performance.
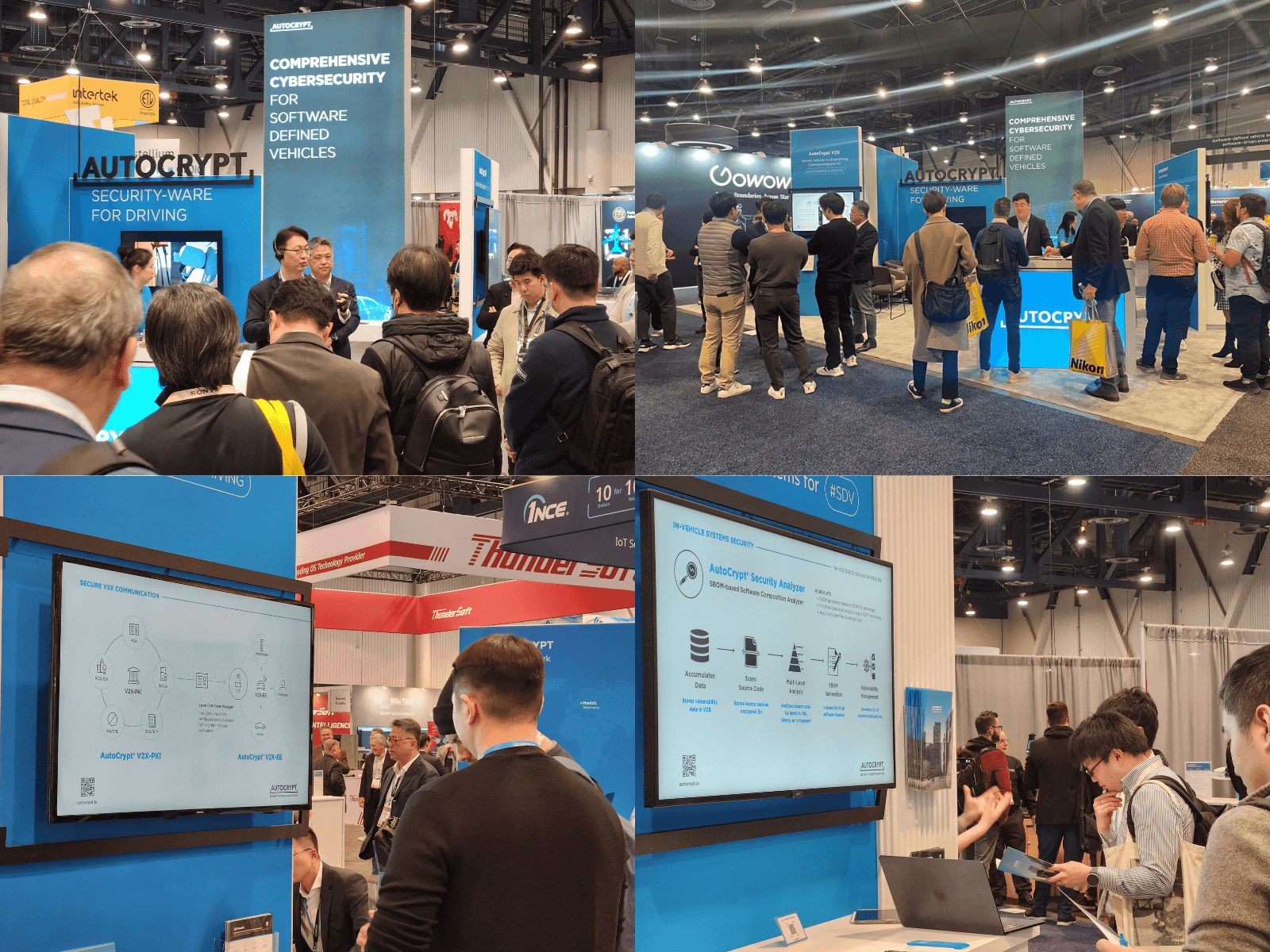
In response to this shift, cyber resilience gains strategic importance. Cyber resilience refers to the ability of a system to withstand, recover from, and continue operating despite cyberattacks. It is no longer an enhancement, but a core requirement for ensuring that complex, interconnected systems remain stable, predictable and operable in real-world environments.
Enhancing User Trust through Cyber Resilience
While cyber resilience defines how systems operate under failure, its ultimate impact is measured in user trust. Research from University of New South Wales (Link) highlights that trust in autonomous vehicles is highly sensitive to cyber incidents, where even a single attack can undermine public confidence at scale. The study further emphasizes that trust is shaped by how effectively organizations prepare for and respond to such events in ways that align with user expectations.
In this context, cybersecurity maturity becomes a critical determinant of adoption. Organizations that fail to demonstrate adequate preparedness risk eroding public confidence, which can slow adoption, reduce usage, and ultimately hinder the broader development of the autonomous mobility ecosystem.
Recognizing the relationship between user trust and long-term business viability, systems must incorporate safeguards that reinforce user confidence. This includes enabling predictable behavior, supporting controlled responses and maintaining stable operation throughout the system lifecycle. As complexity increases across interconnected environments, trust evolves into a system-level requirement, extending beyond individual products to vehicles, services and networks.
Enabling this shift requires more than optimizing individual technologies; it demands an integrated infrastructure approach that operates seamlessly across system boundaries — an approach that AUTOCRYPT is actively advancing. Through CRA-aligned regulatory readiness, in-vehicle cybersecurity solutions, and V2X security services, AUTOCRYPT supports OEMs and Tier 1 suppliers in building cyber-resilient systems, representing a natural evolution beyond traditional cybersecurity.
Additional Resources
- Learn more about our CRA Compliance solution: https://autocrypt.io/solutions/cyber-resilience-act-cra/
- Learn more about our Products and Offerings: https://autocrypt.io/all-products-and-offerings/